GitLab Integration with LDAP/ADDS
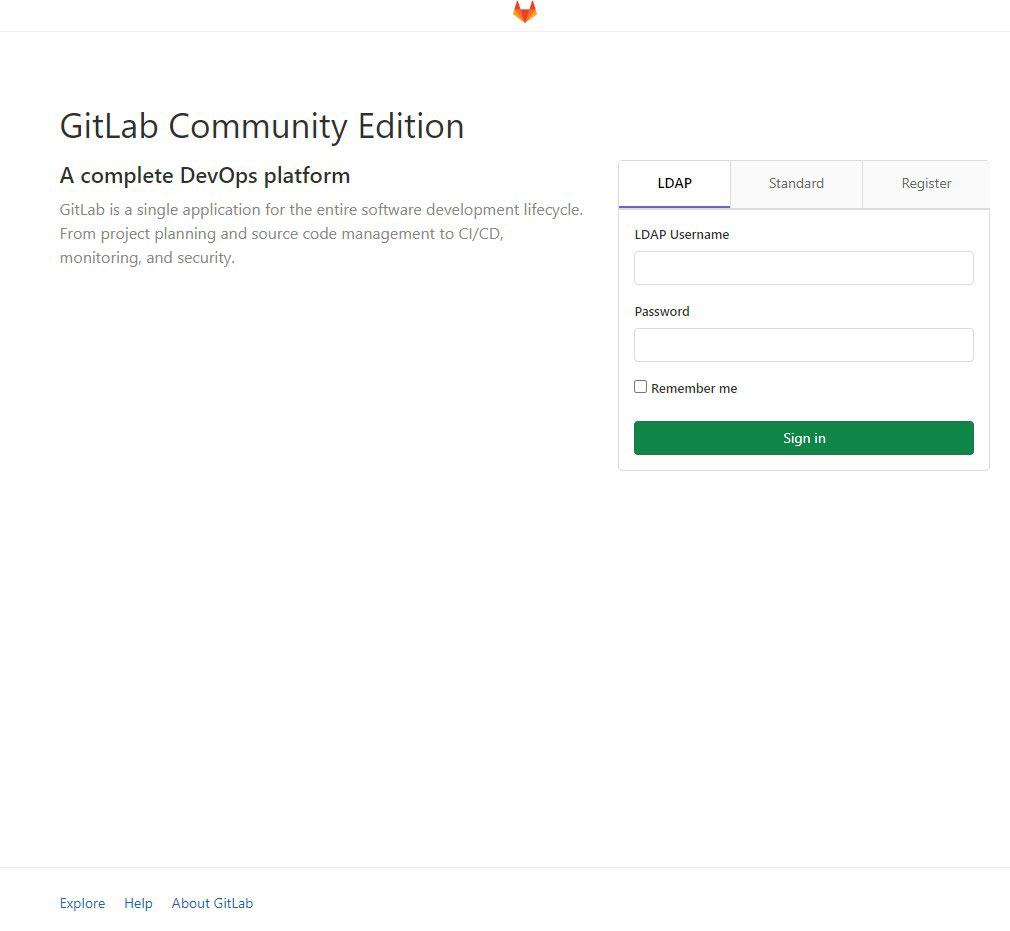
To enable LDAP and/or AD Authentication on GitLAB you must ensure the following:
- Have a service account that can read the LDAP Tree
- If you have a Samba LDAP Controller disable strong auth by entering the following parameter in the global section
ONLY RECOMMENDED FOR TESTING OR ‘SAFE’ ENVIRONMENTS
- To disable strong auth in LDAP add the following to the samba config file (global section):
ldap server require strong auth = no
It’s recommendable to disable the interactive login for this account on the Samba LDAP DC
or Windows AD, as its a service account.
Create an OU and a Security Group for the LDAP/AD Users you’ll be
adding to GitLAB
Once that is done you can modify the gitlab.rb config file (in /etc/gitlab) by uncommenting the following settings.
To check if the user can read the LDAP Tree you can use the following command on a shell console
$ ldapsearch -x -LLL -h ldapserver.yourdomain.com -D "gitlabldap" -w password -b "dc=yourdomain,dc=com" -s sub "(&(memberOf=CN=gitlab,OU=gitlab,DC=yourdomain,DC=com))" sAMAccount
### LDAP Settings
###! Docs: https://docs.gitlab.com/omnibus/settings/ldap.html
###! **Be careful not to break the indentation in the ldap_servers block. It is
###! in yaml format and the spaces must be retained. Using tabs will not work.**
gitlab_rails['ldap_enabled'] = true
gitlab_rails['prevent_ldap_sign_in'] = false
###! **remember to close this block with 'EOS' below**
gitlab_rails['ldap_servers'] = YAML.load <<-'EOS'
main: # 'main' is the GitLab 'provider ID' of this LDAP server
label: 'LDAP'
host: 'ldapserver'
port: 389
uid: 'sAMAccountName'
bind_dn: 'CN=gitlabldap,OU=oucontainername,DC=yourdomain,DC=com'
password: 'yourpassword'
encryption: 'plain' # "start_tls" or "simple_tls" or "plain"
verify_certificates: true
smartcard_auth: false
active_directory: false
allow_username_or_email_login: true
lowercase_usernames: true
block_auto_created_users: false
base: 'DC=yourdomain,DC=com'
attributes:
username: ['uid', 'userid', 'sAMAccountName']
email: ['mail', 'email', 'userPrincipalName']
name: 'cn'
first_name: 'givenName'
last_name: 'sn'
user_filter: '(&(memberOf=CN=gitlab,OU=gitlab,DC=yourdomain,DC=com))'
# ## EE only
# group_base: ''
# admin_group: ''
# sync_ssh_keys: false
#
# secondary: # 'secondary' is the GitLab 'provider ID' of second LDAP server
# label: 'LDAP'
# host: '_your_ldap_server'
# port: 389
# uid: 'sAMAccountName'
# bind_dn: '_the_full_dn_of_the_user_you_will_bind_with'
# password: '_the_password_of_the_bind_user'
# encryption: 'plain' # "start_tls" or "simple_tls" or "plain"
# verify_certificates: true
# smartcard_auth: false
# active_directory: true
# allow_username_or_email_login: false
# lowercase_usernames: false
# block_auto_created_users: false
# base: ''
# user_filter: ''
# ## EE only
# group_base: ''
# admin_group: ''
# sync_ssh_keys: false
EOS
I recommend setting the “block_auto_created_users” flag to false so
that you don’t have to manually create each user you add to the LDAP/AD
Gitlab group.
After you save and quit you can now execute the following on a shell console
$ gitlab-ctl reconfigure && gitlab-rake gitlab:ldap:check
The output should be the following:
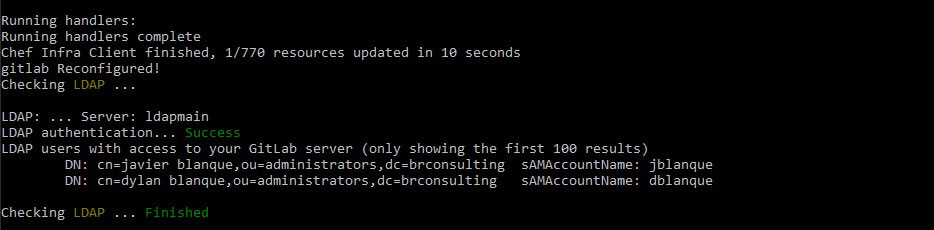
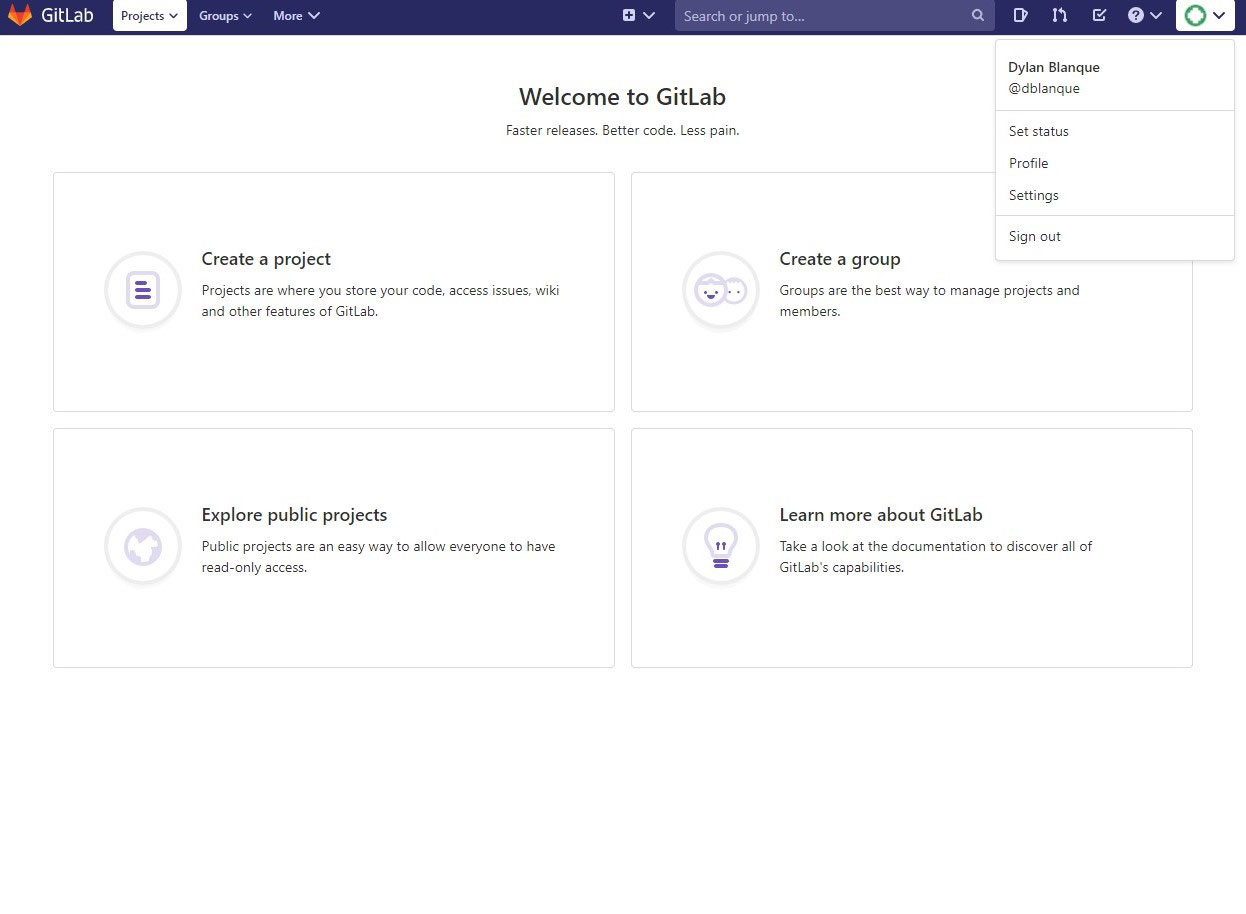
You should now be able to log into your GitLAB CE server with LDAP / Active Directory Credentials!